pwn小知识库
https://www.yuque.com/cyberangel/rg9gdm
1 | fmtstr_payload(num,{x_addr:str_addr}) |
1 | patchelf --set-interpreter ./glibc-all-in-one-master/libs/2.23-0ubuntu11.3_amd64/ld-2.23.so ./test1 |
1 | cat old_list | grep 2.32 |
1 | ./download_old 2.32-0ubuntu3_amd64 |
1 | ┌──(pwn_env)─(root㉿kali)-[/home/kali/Desktop] |
1 | killall -9 main |
1 | chmod 777 ./file |
1 | su root //passwd:123qwe |
1 | source /home/kali/pwn_env/bin/activate |
1 | ropper -f ./pwn1 --search "ebp|ret" |
1 | ropper -f ./BUU23 --string sh --all |
1 | objdump -d ./pwn1 | grep -A 10 "secret" |
- pwntools - 完整可用(刚刚验证成功)
- one_gadget - 已安装
- seccomp-tools - 已安装
- LibcSearcher - 已下载文件
- gdb + pwndbg - 已安装
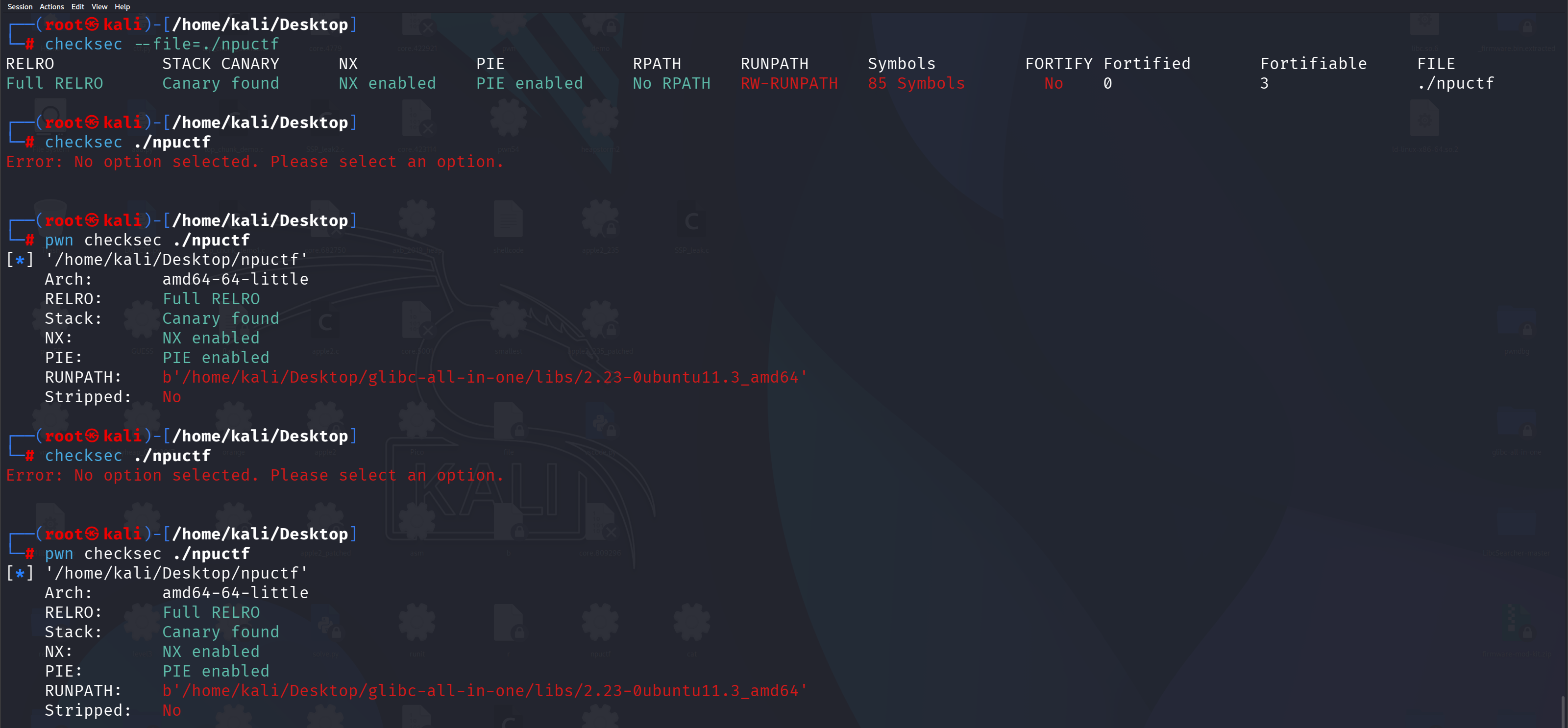
- checksec, strace, patchelf - 已安装
CTFshow—PWN入门—会员特权
| 靶场序号 | 模块 | 攻击面 | 攻击手段 |
|---|---|---|---|
| 1-36 | 前置基础模块 | 计组原理 | ssh远程连接、配置pwn环境 |
| 汇编基础 | 读汇编指令,数据的传送与访问以及了解栈与函数的调用 | ||
| 二进制文件基础 | 从源码到可执行文件 | ||
| Linux相关基础命令 | 基本命令的使用与绕过 | ||
| Linux安全机制 | 保护机制的实现与利用 | ||
| 37-90 | 栈溢出与ROP模块 | 栈溢出(Stack Overflow) | ret2text |
| ret2shellcode | |||
| ret2syscall | |||
| ret2libc | |||
| 返回导向编程(ROP) | ROP | ||
| BROP | |||
| SROP | |||
| ret2dl-resolve | |||
| Stack pivoting | |||
| 91-100 | 格式化字符串漏洞模块 | 格式化字符串漏洞(Format String Vulnerabilities) | 程序崩溃 |
| 栈数据泄露 | |||
| 任意地址内存泄露 | |||
| 栈数据覆盖 | |||
| 任意地址内存覆盖 | |||
| 101-110 | 整数安全模块 | 整数安全(Integer Security) | 整数溢出(Integer Overflow) |
| 整数下溢(Integer Underflow) | |||
| 整数截断(Integer Truncation) | |||
| 整数比较(Integer Comparison) | |||
| 整数转换(Integer Conversion) | |||
| 标志位操作(Flag Manipulation) | |||
| 随机数生成(Random Number Generation) | |||
| 111-134 | Bypass安全机制 | RELRO(Relocation Read-Only) | No RELRO 全关时的安全问题 |
| Partial RELRO 部分开启时的安全问题 | |||
| Full RELRO 全开时的安全问题 | |||
| Stack Canaries(金丝雀保护) | No Canary Found 时的安全问题 | ||
| 覆盖低字节泄露 | |||
| 格式化字符串泄露 | |||
| SSP (Stack Smashing Protector) Leek | |||
| 劫持 __stack_chk_fail 函数 | |||
| one_by_one 爆破 canary | |||
| 覆盖TLS中储存的canary值 | |||
| C++异常机制绕过canary | |||
| 栈地址任意写绕过canary检查 | |||
| 数组下标越界 | |||
| No-eXecute (NX) | No Nx 利用 | ||
| Nx 绕过 | |||
| ASLR和PIE | 地址空间布局随机化 | ||
| 位置无关可执行代码与文件 | |||
| FORTIFY_SOURCE | 危险函数替换机制 | ||
| 135-305 | 堆模块 | 堆利用(Heap Exploitation) | 堆溢出(Heap Overflow) |
| 重复释放(Double Free) | |||
| 使用已释放的内存(Use-After-Free,UAF) | |||
| 未初始化的指针(Uninitialized Pointer) | |||
| 堆块重叠(Heap Block Overlapping) | |||
| fastbin attack | |||
| tcache attack | |||
| Unsorted Bin into Stack | |||
| Large Bin Attack | |||
| House of 系列 | house of spirit | ||
| house of einherjar | |||
| house of force | |||
| house of lore | |||
| house of orange | |||
| house of rabbit | |||
| house of roman | |||
| house of pig | |||
| house of banana | |||
| house of emma | |||
| house of kiwi | |||
| house of husk | |||
| house of corrosion | |||
| house of storm | |||
| house of atum | |||
| House of IO | |||
| House of apple1 2 3 | |||
| house of gods … | |||
| 306-325 | 利用技巧 | PWN trick | one-gadget 和 通用 gadget |
| Return-to-scu | |||
| DynELF泄露函数地址 | |||
| SSP Leak | |||
| environ泄露栈地址 | |||
| vsyscall的利用 | |||
| 劫持hook函数 | |||
| _IO_FILE 结构利用 | |||
| … | |||
| 326-330 | 其他漏洞利用 | 逻辑漏洞利用 | 二级指针利用 |
| 未初始化验证 | |||
| 泄露特定信息 | |||
| WEB-PWN | |||
| 331-355 | 异构PWN | Other architectures PWN | LLVM IR & LLVM Pass & VM |
| Windows PWN | |||
| MIPS PWN | |||
| ARM PWN | |||
| RISC-V PWN | |||
| 356-360 | 内核PWN | Kernel PWN 入门 | 缓冲区溢出 |
| 内核堆利用 | |||
| 内核ROP | |||
| 内核模块利用 | |||
| 内核ROP链构建 | |||
| 361-432 | 大赛题目训练 | 国内外大赛题目复现 | - |
(Return-Oriented Programming)
会员权益
- 帮助中心
- 效率指南
更新: 2026-04-26 13:35:25
原文: https://www.yuque.com/idcm/wnemg9/rulhi28n88zcqk7p
